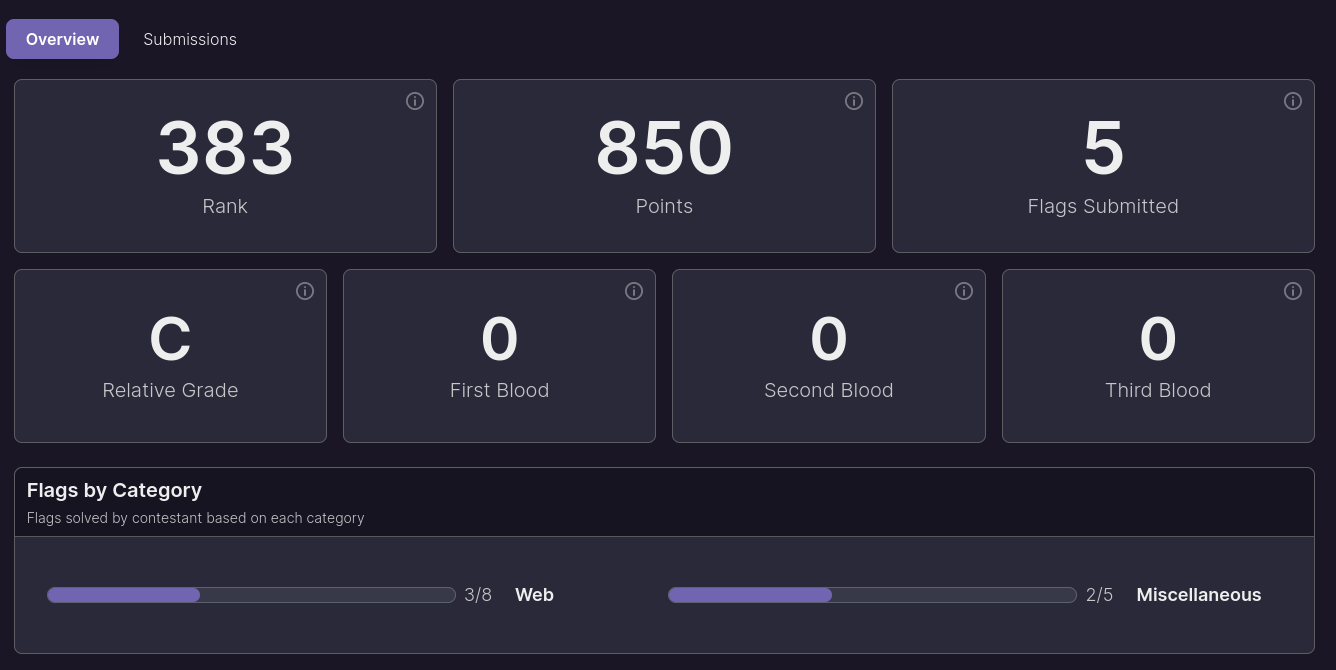
Description
Files can always be changed in a secret way. Can you find the flag? cat.jpg
Solution
Check out the details of the attached image file.
exiftool can be used.
exiftool cat.jpgThen, we get the result as below.
eoniboogie-picoctf@webshell:~$ exiftool cat.jpg
ExifTool Version Number : 12.40
File Name : cat.jpg
Directory : .
File Size : 858 KiB
File Modification Date/Time : 2024:04:03 00:26:25+00:00
File Access Date/Time : 2024:04:03 00:27:02+00:00
File Inode Change Date/Time : 2024:04:03 00:26:25+00:00
File Permissions : -rw-rw-r--
File Type : JPEG
File Type Extension : jpg
MIME Type : image/jpeg
JFIF Version : 1.02
Resolution Unit : None
X Resolution : 1
Y Resolution : 1
Current IPTC Digest : 7a78f3d9cfb1ce42ab5a3aa30573d617
Copyright Notice : PicoCTF
Application Record Version : 4
XMP Toolkit : Image::ExifTool 10.80
License : cGljb0NURnt0aGVfbTN0YWRhdGFfMXNfbW9kaWZpZWR9
Rights : PicoCTF
Image Width : 2560
Image Height : 1598
Encoding Process : Baseline DCT, Huffman coding
Bits Per Sample : 8
Color Components : 3
Y Cb Cr Sub Sampling : YCbCr4:2:0 (2 2)
Image Size : 2560x1598
Megapixels : 4.1License looks like base 64 encoded. Let’s decode it.
echo cGljb0NURnt0aGVfbTN0YWRhdGFfMXNfbW9kaWZpZWR9 | base64 -dpicoCTF{the_m3tadata_1s_modified}